Attackers are handing off access in 22 seconds, Mandiant finds
Exploits remain the leading entry point for attackers for the sixth consecutive year, according to Mandiant’s M-Trends 2026 report, which draws on more than 500,000 hours of incident response work conducted in 2025. The data shows attackers speeding up their internal hand-offs, shifting away from email phishing, and targeting backup and virtualization infrastructure with greater precision.
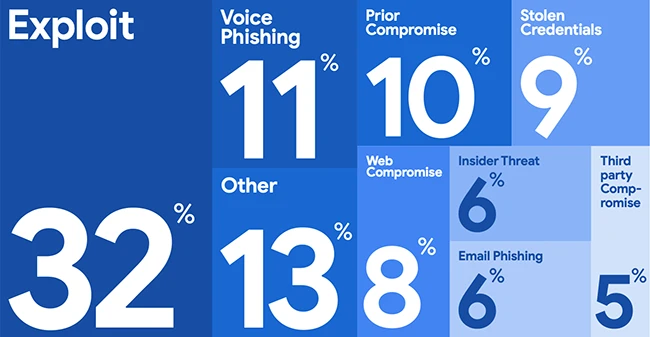
Initial infection vector 2025 (Source: Mandiant)
Voice phishing surges as email phishing continues to decline
Voice phishing climbed to the second-most common initial infection vector in 2025, appearing in 11% of Mandiant investigations where a vector could be identified. Exploits remained first at 32%. Email phishing, which was the dominant social engineering vector just a few years ago, has seen a sustained decline and now represents a fraction of its former share.
The distinction matters for defenders: interactive social engineering methods require live human engagement and are significantly more resistant to automated technical controls than volume-based email campaigns. Different detection strategies are required.
In one campaign spanning the first half of 2025, UNC6040 used voice phishing to convince targets to hand over credentials and authorize attacker-controlled versions of legitimate SaaS applications. Victims later received ShinyHunters-branded extortion notes. UNC3944, a financially motivated cluster with overlap with publicly reported Scattered Spider activity, continued targeting help desk staff by impersonating employees requesting password resets and multi-factor authentication changes.
The access hand-off is getting faster
A growing share of Mandiant investigations followed a division-of-labor model in which one threat cluster gains initial access and transfers it to a separate group for follow-on operations. This pattern appeared in 9% of 2025 investigations, up from 4% in 2022. The time between initial compromise and the hand-off has collapsed.
In 2022, the median time between initial access and hand-off was more than eight hours. In 2025, that figure fell to 22 seconds. Initial access partners now commonly deliver malware directly on behalf of secondary groups, bypassing underground forum sales and compressing the window defenders have to act.
One documented case involved UNC1543, which distributes the FAKEUPDATES JavaScript downloader through drive-by downloads, and UNC2165, a financially motivated cluster with significant overlap with the group publicly reported as Evil Corp. In a 2025 investigation, roughly 70 minutes elapsed between the FAKEUPDATES infection and UNC2165’s earliest interactive activity. UNC2165 ultimately destroyed backups and deployed RansomHub ransomware across Windows and virtual management servers.
Organizations focused exclusively on detecting high-impact tactics may lack detections for the low-impact techniques initial access partners use. Stopping a compromise at the single-system stage is significantly easier than recovering from follow-on activity.
Global dwell time rises to 14 days
Global median dwell time was 14 days in 2025, up from 11 days in 2024, driven largely by long-term espionage intrusions and North Korean IT worker operations. Both categories had a median dwell time of 122 days, or roughly four months.
More incidents went undiscovered for intermediate periods (one week to six months) compared to 2024, a shift the report attributes to groups that limit their tooling to what is available in the targeted environment, mimic legitimate administrative behavior, and remove forensic artifacts.
Organizations that detected intrusions internally did so in about nine days. External notification cases took substantially longer — a median of 25 days in 2025, up from 11 days in 2024. Just over half of organizations detected evidence of malicious activity internally in 2025, a meaningful improvement over the prior year.
Ransomware operators target recovery infrastructure
Ransomware-related intrusions accounted for 13% of Mandiant investigations in 2025. Operators have moved beyond dual-threat encryption-and-theft operations toward systematically denying organizations the ability to recover, targeting identity services, virtualization management planes, and backup infrastructure.
Mandiant investigated multiple breaches in which threat actors exploited misconfigured Active Directory Certificate Services (AD CS) templates to create administrator accounts exempt from multi-factor authentication. In other cases, attackers extracted dozens of high-privilege credentials in a single session from enterprise credential vaults, then forced password changes on privileged accounts, locking defenders out of emergency access during a crisis.
Attackers also compressed and archived Virtual Hard Disks directly on hypervisors, bypassing data loss prevention controls running inside guest operating systems, then deployed ransomware at the hypervisor level by encrypting datastore files. In one documented case, attackers compromised backup management servers, extracted credentials from configuration databases, and wiped millions of backup objects from cloud storage alongside dozens of local system backups.
Prior compromise was the top confirmed initial infection vector for ransomware-related incidents, nearly doubling from the prior year to 30%. The most commonly observed ransomware variant was REDBIKE, known publicly as Akira, followed by AGENDA, known as Qilin. Qilin became the single-most prolific ransomware brand by data leak site volume in 2025.
Three vulnerabilities drove widespread exploitation
The most frequently exploited vulnerabilities in 2025 Mandiant investigations were all zero-days targeting internet-facing enterprise application servers.
CVE-2025-31324, an improper authorization flaw in SAP NetWeaver’s Visual Composer component, allowed unauthenticated file uploads. Multiple threat clusters exploited it as a zero-day before SAP patched it in April 2025, and several suspected PRC-nexus espionage groups exploited it afterward. Post-compromise activity centered on web shell installation and reconnaissance.
CVE-2025-61882, an improper authentication vulnerability in Oracle E-Business Suite, allowed unauthenticated remote code execution. A threat cluster claiming CL0P affiliation sent extortion emails in September 2025 claiming to have stolen documents from Oracle EBS customers. Mandiant identified evidence of successful exploitation as early as August 2025 and attributes the activity to a suspected FIN11 cluster, based on use of the CL0P data leak site and the Java-based GOLDVEIN.JAVA downloader.
CVE-2025-53770, a deserialization vulnerability in Microsoft SharePoint Server, could be chained with CVE-2025-53771 in an exploit known as ToolShell. At least two clusters exploited it as a zero-day, and three more did so after patches shipped in late July. The financially motivated cluster UNC6357 used the SharePoint vulnerabilities to deploy LOCKBIT.WARLOCK ransomware.
GOLDVEIN.JAVA was the most frequently observed malware family across all 2025 investigations. Cobalt Strike BEACON fell to fourth after five consecutive years at the top, its share of observed malware families having shrunk from more than a quarter of investigations in 2021 to just 2% in 2025.
Edge and core network devices are a growing target
The mean time to exploit vulnerabilities has turned negative. GTIG measured an average TTE of 63 days in 2018; by 2024 it had reached -1 day, and in 2025 it is estimated at -7 days, meaning exploitation, on average, begins before a patch is available.
Edge and core network devices have become primary targets for sustained campaigns. These devices often run proprietary operating systems incompatible with enterprise endpoint detection and response tools, creating visibility gaps that sophisticated actors exploit to perform reconnaissance, lateral movement, privilege escalation, and data collection from the device itself.
UNC5807, whose activity is generally consistent with the publicly discussed Salt Typhoon actor, targeted telecommunications organizations by using device-native packet capture functionality to collect credentials from cleartext network protocols, then moving deeper into targeted environments. UNC5221 exploited two separate zero-day vulnerabilities in the same VPN product over a three-month period, deployed in-memory malware to minimize disk artifacts, and tunneled command and control traffic through legitimate third-party services to bypass standard network filtering.
AI in attacks remains incremental
Threat clusters are incorporating AI tools to accelerate reconnaissance, social engineering, and malware development. Mandiant investigated a supply chain compromise involving the QUIETVAULT credential stealer, which checks for AI command-line tools on compromised machines and, if found, executes prompts to locate configuration files and harvest developer tokens.
Malware families including PROMPTFLUX and PROMPTSTEAL actively query large language models during execution to support evasion. State-sponsored and financially motivated actors are using LLMs to shift from mass email campaigns toward personalized, rapport-building social engineering.
The report’s overall assessment: 2025 was not the year where breaches were the direct result of AI. Most successful intrusions continued to stem from human and systemic failures.
Scale: threat clusters and malware families keep growing
The high-tech sector led all industries in share of Mandiant investigations in 2025, surpassing financial services, which had led for the two prior years. Healthcare and business services also appeared consistently near the top.
GTIG began tracking 714 new malware families in 2025, bringing the total to more than 6,000. More than 660 new threat clusters were tracked, pushing the overall total past 5,000. Financially motivated groups made up the largest share of clusters observed in Mandiant investigations, at roughly two-fifths of the total. Cyber espionage groups doubled their share compared to 2024, rising to 16% of observed clusters.
North Korean IT workers using false identities to carry out employment fraud remained a significant and persistent insider threat, with a median dwell time of 122 days and, in several cases, undetected presence lasting more than a year.

Webinar: The True State of Security 2026