Help Net Security

Week in review: Chrome 0-day fixed, npm supply chain attack, LinkedIn data used for AI
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Most enterprise AI use is invisible to security teams Most enterprise AI …

Researchers believe Gamaredon and Turla threat groups are collaborating
ESET Research has discovered evidence of collaboration between the Gamaredon and Turla threat groups. Both groups are linked to Russia’s primary intelligence agency, the FSB, …

The real-world effects of EU’s DORA regulation on global businesses
In this Help Net Security video, Matt Cooper, Director of Governance, Risk, and Compliance at Vanta, discusses the EU’s Digital Operational Resilience Act (DORA) and its …
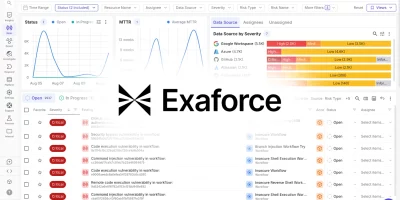
Product showcase: Exaforce – The full lifecycle AI SOC platform
Today’s SOCs face an impossible equation: too much noise, too many gaps, and too few hands. Detection coverage gaps leave companies exposed, false positives overwhelm …

Bots vs. humans? Why intent is the game-changer
In this Help Net Security video, Jérôme Segura, VP of Threat Research at Datadome, explains why intent, not just identifying bots, must be the new focus for cybersecurity …
Arkime: Open-source network analysis and packet capture system
Arkime is an open-source system for large-scale network analysis and packet capture. It works with your existing security tools to store and index network traffic in standard …

What could a secure 6G network look like?
The official standards for 6G are set to be announced by the end of 2029. While the industry is moving towards consensus around how the 6G network will be built, it also needs …

Why neglected assets are the hidden threat attackers love to find
In this Help Net Security video, Tim Chase, Tech Evangelist at Orca Security, explores one of the most overlooked cybersecurity risks: neglected assets. From forgotten cloud …

Week in review: Salesloft Drift breach investigation results, malicious GitHub Desktop installers
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Salesloft Drift data breach: Investigation reveals how attackers got in The …

HybridPetya: (Proof-of-concept?) ransomware can bypass UEFI Secure Boot
ESET researchers have discovered HybridPetya, a bootkit-and-ransomware combo that’s a copycat of the infamous Petya/NotPetya malware, augmented with the capability of …

The state of DMARC adoption: What 10M domains reveal
In this Help Net Security video, John Wilson, Senior Fellow, Threat Research at Fortra, explores the state of DMARC adoption across the top 10 million internet domains. He …
Garak: Open-source LLM vulnerability scanner
LLMs can make mistakes, leak data, or be tricked into doing things they were not meant to do. Garak is a free, open-source tool designed to test these weaknesses. It checks …
Featured news
Resources
Don't miss
- Open-source privacy proxy masks PII before prompts reach external AI services
- cPanel zero-day exploited for months before patch release (CVE-2026-41940)
- Cisco releases open-source toolkit for verifying AI model lineage
- Nine-year-old Linux kernel flaw enables reliable local privilege escalation (CVE-2026-31431)
- 88% of self-hosted GitHub servers exposed to RCE, researchers warn (CVE-2026-3854)