
32% of top-exploited vulnerabilities are over a decade old
Exploitation timelines continued to compress in enterprise environments, with newly disclosed flaws reaching active use almost immediately and older weaknesses remaining …

Clipping Scripted Sparrow’s wings: Tracking a global phishing ring
Between June 2024 and December 2025, Fortra analysts tracked a persistent business email compromise (BEC) operation that we have now classified as Scripted Sparrow. The group …
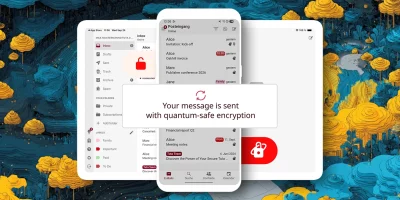
Product showcase: Tuta – secure, encrypted, private email
Tuta, formerly known as Tutanota, is built for anyone who wants email that stays private. Instead of treating encryption like a bonus feature, the service encrypts almost …

Proxmox Mail Gateway: Open-source email security solution reaches version 9.0
First released in 2005, the open-source Proxmox Mail Gateway has become a widely adopted mail proxy, positioned between the firewall and the internal mail server to stop …

Microsoft urges admins to plug severe Exchange security hole (CVE-2025-53786)
“In an Exchange hybrid deployment, an attacker who first gains administrative access to an on-premises Exchange server could potentially escalate privileges within the …

Microsoft introduces protection against email bombing
By the end of July 2025, all Microsoft Defender for Office 365 customers should be protected from email bombing attacks by default, Microsoft has announced on Monday. What is …

Employees repeatedly fall for vendor email compromise attacks
In just 12 months, attackers attempted to steal more than $300 million via vendor email compromise (VEC), with 7% of engagements coming from employees who had engaged with a …

Only 1% of malicious emails that reach inboxes deliver malware
99% of email threats reaching corporate user inboxes in 2024 were response-based social engineering attacks or contained phishing links, according to Fortra. Only 1% of …

Nine out of ten emails are spam
Now, more than ever, users can fall prey to word-perfect AI-created phishing campaigns, subtle BEC messages that sound remarkably like the sender, and highly convincing ploys …

Threat actors are stepping up their tactics to bypass email protections
Although most organizations use emails with built-in security features that filter out suspicious messages, criminals always find a way to bypass these systems. With the …

Security measures fail to keep up with rising email attacks
Organizations must reassess their email security posture as incidents continue to escalate, leading to financial losses. Key findings reveal a significant increase in email …

Why the automotive sector is a target for email-based cyber attacks
While every organization across every vertical is at risk of advanced email attacks, certain industries periodically become the go-to target for threat actors. In this Help …