cybersecurity

Finding connection and resilience as a CISO
With sensitive information to protect and reputational risk always in the background, it isn’t easy for security leaders to have open conversations about what’s working and …

AI isn’t taking over the world, but here’s what you should worry about
In this Help Net Security video, Josh Meier, Senior Generative AI Author at Pluralsight, debunks the myth that AI could “escape” servers or act on its own. He explains how …

Maritime cybersecurity is the iceberg no one sees coming
Maritime transport, the backbone of global trade, is adapting to shifting economic, political, and technological conditions. Advances in technology have improved efficiency, …

Can AI make threat intelligence easier? One platform thinks so
When analysts at RH-ISAC found themselves spending 10 hours a week just collecting threat intelligence, they knew their process wasn’t sustainable. They were manually tracking …

How CISOs are balancing risk, pressure and board expectations
AI has moved to the top of the CISO agenda. Three in five CISOs see generative AI as a security risk, with many worried about sensitive data leaking through public tools. At …

AI is becoming a core tool in cybercrime, Anthropic warns
A new report from Anthropic shows how criminals are using AI to actively run parts of their operations. The findings suggest that AI is now embedded across the full attack …

AI Security Map: Linking AI vulnerabilities to real-world impact
A single prompt injection in a customer-facing chatbot can leak sensitive data, damage trust, and draw regulatory scrutiny in hours. The technical breach is only the first …

How compliance teams can turn AI risk into opportunity
AI is moving faster than regulation, and that creates opportunities and risks for compliance teams. While governments work on new rules, businesses cannot sit back and wait. …

Hottest cybersecurity open-source tools of the month: August 2025
This month’s roundup features exceptional open-source cybersecurity tools that are gaining attention for strengthening security across various environments. Buttercup: …
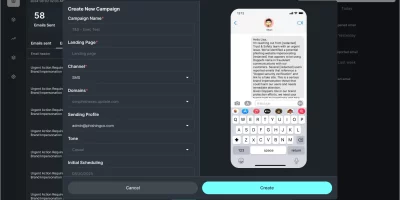
What CISOs can learn from Doppel’s new AI-driven social engineering simulation
Doppel has introduced a new product called Doppel Simulation, which expands its platform for defending against social engineering. The tool uses autonomous AI agents to create …

Protecting farms from hackers: A Q&A with John Deere’s Deputy CISO
Agriculture is a connected, software-driven industry where cybersecurity is just as essential as tractors and harvesters. From embedded hardware in smart fleets to defending …
The energy sector has no time to wait for the next cyberattack
The energy sector remains a major target for cybercriminals. Beyond disrupting daily routines, a power outage can undermine economic stability and public safety. Rising demand …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)