Infosec products of the month: February 2023
Here’s a look at the most interesting products from the past month, featuring releases from: Arkose Labs, Cequence Security, CyberGRX, CyberSaint, Deepwatch, DigiCert, Finite State, FireMon, Hornetsecurity, HYCU, KELA, Lacework, Malwarebytes, Netography, Neustar Security Services, Nudge Security, OPSWAT, SecuriThings, Trulioo, Veeam Software, and Xcitium.


DigiCert releases new unified approach to trust management
DigiCert Trust Lifecycle Manager offers something that enterprises need but do not currently have: it unifies CA-agnostic certificate lifecycle management, PKI services and public trust issuance for a full-stack solution that helps companies discover all of their certificates and manage them efficiently.


Hornetsecurity unveils two tools to counter rise in phishing attacks and malicious links
Hornetsecurity launched two new tools – the QR Code Analyzer and Secure Links – to combat growing cyber threats. QR Code Analyzer is able to detect QR codes embedded in other images that can re-route to other malicious sites and Secure Links runs all email links through a secure analyzer before enabling the recipient to safely open the link.


HYCU R-Cloud protects all business-critical apps from on-premises to SaaS
HYCU R-Cloud provides businesses with a comprehensive visualization of their entire data estate and protection status via auto-discovery and mapping of all applications and services – SaaS, PaaS, DBaaS, public, and private cloud. Organizations get a detailed and holistic view of their business-critical data and their protection status.


KELA launches cyber intelligence platform to empower proactive digital crime prevention
KELA launched a new and consolidated cyber intelligence platform, consisting of a new intuitive user interface and four complementary modules: Threat Landscape, Monitor, Hunt, and Tactical Intelligence. The platform provides real, actionable intelligence to support various security teams across an organization in their efforts to uncover threats and proactively prevent digital crimes.


Trulioo identity verification platform helps businesses achieve regulatory compliance
Trulioo launched a global identity platform for person and business verification. By using a suite of native verification services in a single, comprehensive platform, businesses can streamline their verification processes and reduce the number of vendors they use.


Arkose Labs unveils SMS Toll Fraud online ROI calculator
Arkose Labs has launched a new SMS Toll Fraud online ROI calculator that enables banks, e-commerce companies, and telcos to estimate the potential cost savings associated with stopping SMS Toll Fraud and helps them make informed decisions about their cybersecurity strategy.


OPSWAT MetaDefender Kiosk K2100 secures critical networks in challenging environments
The OPSWAT MetaDefender Kiosk K2100 is a portable solution for protecting critical systems against uncontrolled media and malware. It prevents potential data breaches and regulatory compliance violations by detecting and blocking sensitive data/personally identifiable information (PII) with OPSWAT’s Proactive Data Loss Prevention (DLP) technologies.


Deepwatch SecOps Platform enhancements detect and contain identity threats
Deepwatch announced new service offerings to speed the detection and containment of threats across the enterprise. Centered on advanced threat analytics, dynamic content libraries, and integrations with leading security tools, Deepwatch’s managed detection and response services (MDR, MXDR, and others) provide customers with an “always on” modern SOC that continuously evolves to combat the dynamic threat landscape.


Cequence Security API Security Testing uncovers and remediates API vulnerabilities
API Security Testing detects security risks in pre-production APIs, such as shadow API endpoints, sensitive data exposure and the rest of the OWASP API Top 10 risks so that security teams can remediate them before the APIs are released to production.

Neustar Security Services UltraPlatform protects enterprises’ digital assets
UltraPlatform unifies these cloud-based online functions that are essential to maintaining and safeguarding a company’s digital presence against countless threats and attacks, delivering them as bundled solutions to meet the needs of organizations of any size. Customers can choose from a range of customizable options that deliver DNS, DDoS protection and WAF services, based on the specific needs of their organization.


SecuriThings Managed Service Platform secures physical security devices
With SecuriThings’ Managed Service Platform, MSPs can now offer customers the option of outsourcing the management and maintenance of their physical security devices to a team of experts. This includes automating critical maintenance tasks like firmware upgrades, password rotations, vulnerability detection and more.


CyberSaint Executive Dashboard empowers CISOs to take control of cyber risk communication
The Executive Dashboard is the latest in a line of features offered by CyberSaint through its CyberStrong platform. The Executive Dashboard allows CISOs to present their cyber risk posture to the rest of the C-suite and Board of Directors in a credible, financially quantifiable manner that enables informed decision-making.


Finite State releases Next Gen Platform for software supply chain security
Finite State has released Next Generation Platform featuring extended SBOM management with the ability to ingest and aggregate 120+ external data sources. The new platform gives Application and Product Security teams a unified and prioritized risk view with visibility across the software supply chain lifecycle to scale operations through continuous, next-generation risk management.


FireMon Policy Analyzer combats firewall misconfigurations
FireMon Policy Analyzer, a complimentary firewall assessment tool, provides organizations with a comprehensive diagnostic report outlining the health of a firewall policy. It also offerss several downloadable reports including overly permissive access, policy clean up, and high-risk access for additional insights and remediation recommendations.


Veeam Data Platform improves business resiliency in the case of disaster or cyberattacks
The Veeam Data Platform, which includes Veeam Backup & Replication (VBR) v12, provides secure backup and recovery that keeps business running. It brings together the latest features offered from Veeam into a single solution that is offered in three enterprise-grade editions for protecting Cloud, Virtual, Physical, SaaS and Kubernetes applications across expanding IT environments.


Malwarebytes Application Block restricts access to outdated and unsafe apps
Malwarebytes has added Malwarebytes Application Block to its Nebula and OneView endpoint protection platforms. IT security teams can use Application Block’s dashboard to understand what applications are being blocked in real-time, as well as its reporting features to meet key compliance requirements and navigate increasing data protection regulations.


Xcitium ZeroDwell Containment isolates all unknown or suspect code entering an organization
Xcitium’s ZeroDwell technology, utilizing patented kernel-level API virtualization, prevents unknown malware from accessing critical system resources that cause damage, while providing complete use of the unknown file or application.


CyberGRX Portfolio Risk Findings enables customers to identify riskiest vendors
CyberGRX launched a new capability, Portfolio Risk Findings, allowing customers to gain visibility into their organization’s specific control coverages gapped by the riskiest third parties through the lens of any framework or threat profile.


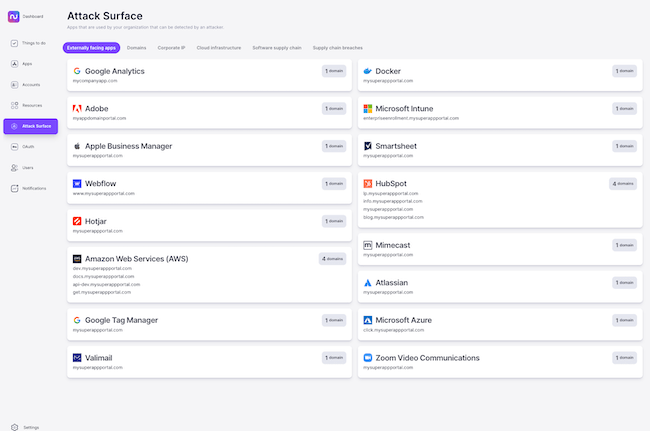
Nudge Security launches SaaS attack surface management capabilities
Nudge Security adds multiple new SaaS attack surface management capabilities to its platform, including SaaS supply chain breach notifications, OAuth risk scoring, and a SaaS attack surface dashboard so customers can know if they’re in the blast radius of a breach.

Netography Fusion enhancements provide real-time visibility of all social media traffic
With Netography Fusion’s operational governance for social media, teams now have the mechanisms they need to automate a continuous approach to testing the efficacy of their security controls against cyber threats and organizational policy.


Lacework releases composite alerts feature to help customers identify and remediate threats
Composite alerts combine human intelligence from Lacework Labs about prevalent attack sequences and tactics with automatic correlation of numerous events, including low criticality data from disparate sources.


