Infosec products of the month: March 2022
Here’s a look at the most interesting products from the past month, featuring releases from: Actiphy, Anomali, AvePoint, Ciphertex Data Security, Contrast Security, Critical Start, CybeReady, Dasera, Deepfence, Dtex Systems, Elastic, Endace, Enzoic, ExtraHop, Imperva, MetricStream, Nebulon, NICE Actimize, Ostrich Cyber-Risk, Palo Alto Networks, Perimeter 81, PKI Solutions, Progress, Rapid7, Reciprocity, Secret Double Octopus, SEON, Sonrai Security, SpyCloud, Swissbit, Veeam Software, Veriff, and VMware.


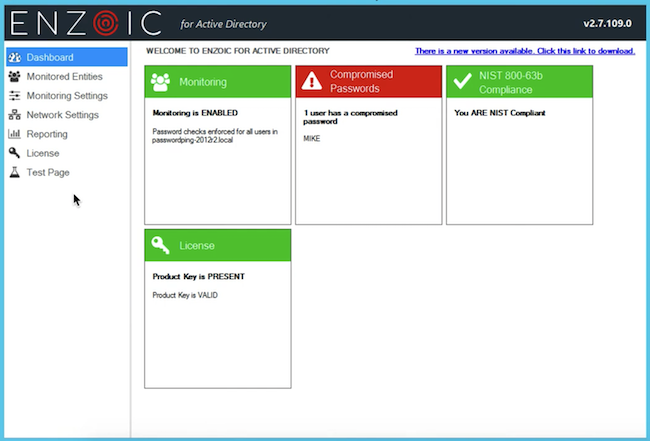
Enzoic’s automated credentials monitoring in Active Directory detects unsafe passwords
Enzoic for Active Directory now detects when an exact username and password combination is exposed, which poses a significant risk to enterprise security. If full credentials are compromised, a more aggressive remediation plan can be automatically activated.

Swissbit iShield FIDO2 protects access to applications and online services
The Swissbit iShield FIDO2 features a robust, industrial quality waterproof plastic housing designed specifically for its extended operating temperature range of -25°C to +70°C. The compact stick (measuring 51.5mm x 18.5mm x 6mm) with a USB-A interface and touch sensor on the reverse also supports NFC for convenient ‘touch-and-go’ authentication with compatible mobile devices.


Perimeter 81 Secure Web Gateway blocks access to specific URLs or categories of websites
Perimeter 81 adds a Secure Web Gateway feature to its Security Services Edge solution, ensuring that company employees are safe from malicious websites and unsafe content, no matter where they are working.


Palo Alto Networks Prisma SASE provides network security and SD-WAN requirements for MSPs
Prisma SASE’s new cloud-based management portal with hierarchical multitenancy capability uses granular role-based access control (RBAC) — that MSPs have lacked until now — to provide the flexibility to manage multiple customers with different needs while providing control across a customer’s entire SASE services lifecycle.


CybeReady Adaptive Training Platform enhancements improve corporate security posture
CybeReady offers a fully-managed security training platform that includes phishing simulations, security awareness, and compliance training capabilities, with built-in expertise already embedded into the training. The platform continuously trains enterprise employees to avoid cyberattacks — in 38 languages across 66 countries worldwide.


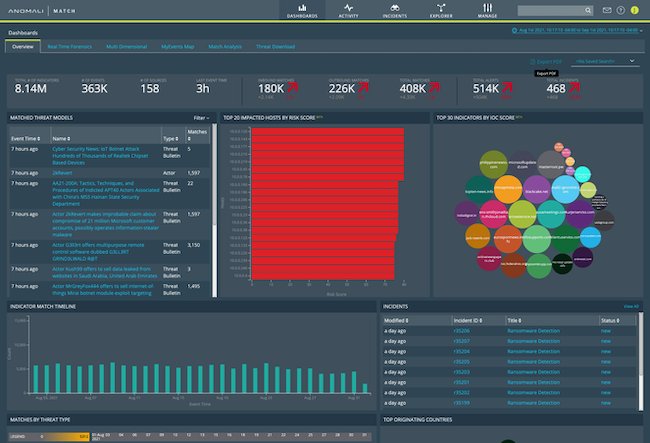
Anomali XDR solution helps enterprises against advanced cyber threats
Anomali launched a cloud-native XDR solution, providing precision detection and optimized response capabilities that extends across their entire security infrastructure. With integrated investigation frameworks, like MITRE ATT&CK, organizations are able to defend throughout the entire attack lifecycle, gaining key insights into where they are in the stage of an attack and relevant intelligence on what to do about it.

VMware enhances end-to-end security offering for cloud-native workloads with container runtime protection
VMware unveiled new container runtime security capabilities that build upon a strong end-to-end security offering to help customers better secure modern applications at scale. Security teams can now accelerate their investigation into incidents impacting endpoints, virtual machine workloads, and containerized workloads.


Endace OSm 7.1 allows analysts to reconstruct and extract files from recorded packet data
OSm 7.1 extends the power of always-on packet recording to multi-tenant environments such as MSSPs, federal or government organizations securing multiple entities, or large enterprises with multiple divisions. Multiple entities can now share a common recording infrastructure and each securely search, access and analyze only their own traffic.


Secret Double Octopus expands multifactor authentication offerings to MSP’s and SMB’s
The Octopus Cloud offerings include all of the company’s Full Passwordless MFA solution, Octopus Enterprise, as well as the passwordless-ready traditional MFA offerings offered using the same architecture and components, Octopus Starter and Octopus Pro.


Imperva API Security protects data across legacy and cloud-native applications
Imperva API Security provides protection for Application Programming Interfaces (APIs) in developer environments that often lack adequate security controls and are vulnerable to malicious or inadvertent exposure. The product mitigates the risk of data breaches and data leakage by uncovering shadow APIs, and suggests remediation for software developers and security administrators.


Dasera Mt. Rainier release allows enterprises to scale data protection efforts
The Mt. Rainier release incorporates tailored roles, interfaces, and customized workflows for Data and Compliance team members, all of which save time, streamline cross-functional coordination, and help to detect and eliminate risk as early as possible.


Veeam Backup for Microsoft 365 v6 boosts customers’ data resilience and mitigates SaaS data risks
The backup and recovery solution for Microsoft 365 enables users to securely back up to any location, including on-premises, in a hyperscale cloud, or with a service provider. New features in v6 increase time savings for IT departments due to diminished burden for recovery requests and additional cost savings as a result of more efficient backups.


Elastic introduces platform enhancements to protect customers against advanced cyber threats
Elastic announced enhancements across the Elastic Search Platform and its solutions. New enhancements enable customers to stop advanced cyber threats with new prebuilt detections and data source integrations, and accelerate application development with deeper visibility into serverless architectures and continuous integration and continuous delivery (CI/CD) pipelines.


AvePoint Ransomware Detection identifies suspicious behavior within users’ Microsoft OneDrive
AvePoint launched Ransomware Detection, as part of Cloud Backup for Microsoft 365, to further protect digital collaboration data. After detecting unusual activity, Cloud Backup provides detailed reports to shorten the investigation and flag the areas of question for Customer’s Admin, and if necessary, restores all or specific OneDrive data, recovering business-critical information quickly for Cloud Backup customers.


Reciprocity ROAR Platform enables companies to mitigate risk in business processes
The new Reciprocity ROAR Platform enables companies to protect their most valuable assets, quantify the value of security investments, accelerate business initiatives, and inform leadership on the levels of risk and improvements.


Palo Alto Networks unveils Prisma Cloud Supply Chain Security to reduce code complexity and risk
Prisma Cloud Supply Chain Security helps provide a full stack, full lifecycle approach to securing the interconnected components that make up and deliver cloud native applications. It can help to identify vulnerabilities and misconfigurations in code, including open source packages, infrastructure as code (IaC) files and delivery pipelines, such as version control system (VCS) and CI pipeline configurations


SpyCloud Session Identity Protection prevents fraud from compromised web sessions
SpyCloud launched Session Identity Protection, a transformative early warning system designed to prevent trusted user fraud, one of the hardest forms of fraud to detect. The new offering is powered by SpyCloud’s malware intelligence, which surfaces credentials and session tokens stolen from consumers by prevalent infostealers.


PKI Spotlight detects operational disruptions in PKI and HSM environments
With PKI Spotlight, PKI Solutions intends to provide enterprise organizations with improved outcomes in Operational Resilience, Security Posture Management, Threat Detection, and adoption of Best Practices. It also improves an organization’s security posture management by maintaining the security and integrity of their PKIs with visibility into configurations that can impact identity and encryption systems.


Ciphertex Data Security SecureNAS CX-160KHD-X protects healthcare data from cyber criminals
Ciphertex Data Security is introducing a new SecureNAS CX-160KHD-X model that can store up to 320TB and is powered by its new CX-Linux ZFS operating system. These products provide a new level of safety, security, and portability for vital healthcare information, which is increasingly under attack by hackers desiring to capture and sell this valuable data or to hold it for ransom.


Deepfence ThreatMapper 1.3.0 allows users to scan workloads and hosts for sensitive secrets
The latest version of ThreatMapper extends scanning capabilities to include a security feature called SecretScanner. The addition of secret scanning technology within ThreatMapper enables security teams to schedule scans for both vulnerabilities and secrets in production, assess the risks associated with each, and prioritize remediation accordingly.


Contrast Security adds software supply chain security capabilities to its Secure Code Platform
Contrast Security announced that its Secure Code Platform now integrates software supply chain security across the development lifecycle, from the developer desktop to production systems. The new integration allows enterprises to identify their biggest supply chain risks and defend against them.


Progress WhatsUp Gold reduces the risk of threat actors and infrastructure compromise
WhatsUp Gold 2022 builds on its interactive mapping interface and total ecosystem visibility through integration with Flowmon that surfaces deep network performance insights in a single dashboard. IT operations teams can now simplify troubleshooting with consolidated access to WhatsUp Gold native infrastructure monitoring view combined with advanced network telemetry.


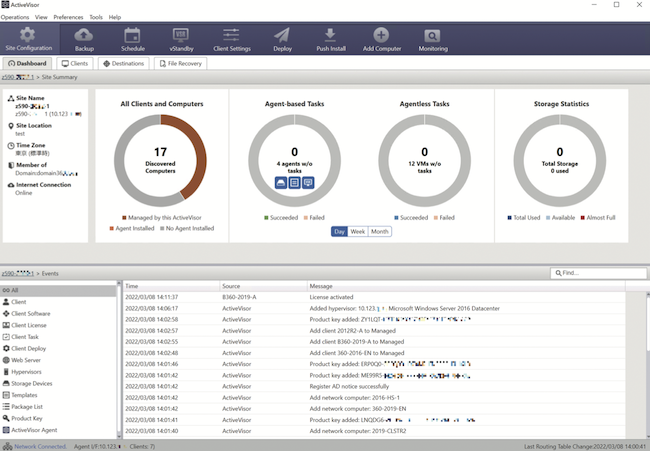
Actiphy ActiveVisor v.7 monitors overall system protection of the backup source PCs
Actiphy released ActiveVisor v.7, a centralized management console, with new features and enhancements supporting ActiveImage Protector 2022. System administrators can substantially reduce workloads by monitoring and managing the backup status and configured backup settings for ActiveImage Protector backup clients from any location.

Ostrich Cyber-Risk Birdseye identifies organization’s financial and operational risks
With Birdseye, organizations can identify their unique risk fingerprint based on a qualitative and in-depth analysis of their current cybersecurity posture and quantify the potential impact of specific vulnerabilities through scenario-based risk tracking.


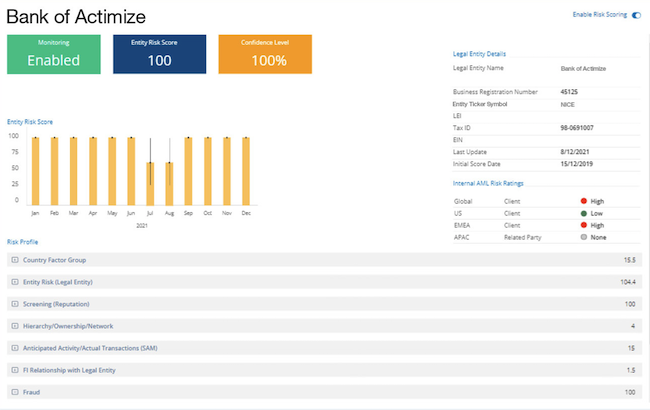
NICE Actimize X-Sight Entity Risk enhances end-to-end enterprise fraud solutions’ effectiveness
NICE Actimize’s X-Sight Entity Risk solution delivers data intelligence from a variety of data sources to ensure an entity profile is always accurate and analyzes entity networks and behaviors to provide a single entity trust score which informs detection and prevention systems to power their analytic precision.

Sonrai Security’s workload security capabilities remove risks across customer’s public cloud
Sonrai Security announced its expansion into Cloud Workload Protection (CWPP), with new capabilities that enable enterprise companies to appropriately react to host-based threats according to their immediate severity and business impact.


AvePoint Cloud Records enhancements improve information lifecycle management for enterprises
AvePoint’s new enhancements automate retention and disposal rules, and provide safe information access retrieval, so that organizations can easily meet requirements and reduce storage overages at the same time.


ExtraHop Reveal(x) 360 for AWS detects malicious activity across workloads
Reveal(x) 360 Cloud Threat Defense for AWS is purpose-built to stop advanced threats like ransomware, software supply chain attacks, and more. This new offering includes VPC Flow Logs and additional protocol analysis, providing both depth and breadth of visibility for threats in AWS.
_360_650.jpg)

DTEX Systems extends scope and protection of Microsoft 365 E5 modules
The behavioral, contextual workforce intelligence provided by DTEX InTERCEPT extends the capabilities of the Microsoft 365 E5 modules to detect and capture intentional data loss incidents, stop intellectual property theft, pinpoint human behavior attribution as well as malware root cause, and prevents the use and misuse of unsanctioned and sanctioned SaaS applications.


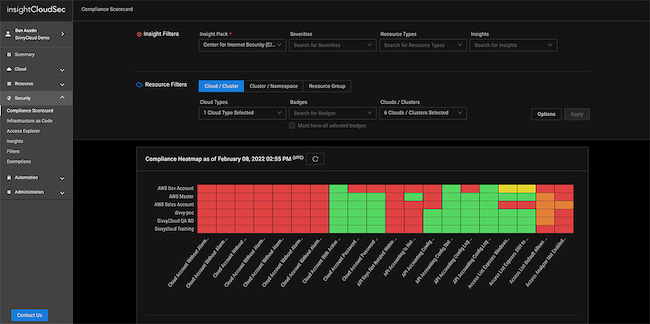
Rapid7 introduces cloud workload protection in InsightCloudSec
Rapid7 announced new cloud workload protection capabilities for InsightCloudSec. These enhancements, which include native vulnerability assessment for container and Kubernetes environments, leverage Rapid7’s vulnerability assessment technology delivered via an agentless experience that is purpose built for cloud-native environments.

Nebulon TimeJump offers ransomware recovery for critical application data and infected operating systems
Nebulon TimeJump provides four-minute restore capabilities not only for critical application data but also infected operating systems, so application infrastructure can be brought back online near-instantly.


Critical Start launches enhanced capabilities for Microsoft 365 Defender to detect user account attacks
Critical Start introduced capabilities around Managed Detection and Response (MDR) services for the Microsoft 365 Defender security suite that protect against phishing, brute force, and cloud application attacks on user credentials.


SEON unveils product updates to help customers battle online fraud
SEON has revamped its product dashboard to allow customers to connect with relevant data and stats in a more intuitive manner. Customers can now add extra widgets to the home screen of their dashboards, which include new location, and filter options.


Veriff launches HR identity verification solution to reduce friction in hiring and recruiting
Veriff has released enhanced identity verification solutions tailored specifically for the human resources and recruiting industries. The suite of solutions streamline and automate the hiring and recruiting process to enable HR teams and staffing firms to cut costs and recruit faster while building trust and creating a smoother application process for candidates.


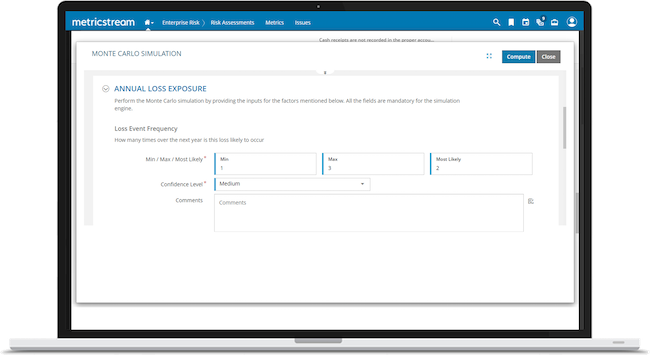
MetricStream Danube enables organizations to quantify risk in monetary terms
The Danube release includes risk quantification, automated compliance across cloud environments, and support for the Task Force on Climate-Related Financial Disclosures (TCFD), providing a framework to assist customers with climate-related financial risk disclosures.