Infosec products of the month: February 2022
Here’s a look at the most interesting products from the last month, featuring releases from: Arista Networks, Blueshift Cybersecurity, Bugcrowd, Cato Networks, Cofense, CoSoSys, Cybellum, Cymulate, Darktrace, DataStax, F5 Networks, Federal Reserve, Forcepoint, Gigamon, Gretel, Juniper Networks, Mandiant, MyCena, NetSPI, Ondato, Orca Security, Ping Identity, Qualys, Runecast, ShiftLeft, Spin Technology, Stellar Cyber, Sumo Logic, SynSaber, Tenable, and Verimatrix.


Qualys minimizes vulnerability risk for organizations with new remediation feature
Qualys announced it is adding advanced remediation to the Qualys Cloud Platform, enabling organizations to fix asset misconfigurations, patch OS and third-party applications, and deploy custom software.


Cymulate Amplify helps companies eliminate critical security blind spots
Cymulate launched Amplify, a human powered offering designed to accelerate the implementation and optimization of their continuous security assurance.


Cato CASB protects enterprises against data breach and cloud-delivered threats
Cato’s CASB solution monitors all enterprise SaaS-bound traffic and provides a detailed shadow IT report which details all applications, both sanctioned and unsanctioned, being accessed and used.


Mandiant Advantage Attack Surface Management allows security teams to operationalize intelligence
Mandiant Advantage Attack Surface Management enables organizations to obtain a deep understanding of their digital footprint and focus on the vulnerabilities that bad actors are most likely to target. Armed with this insight, organizations can take a proactive approach to cyber security, while gaining confidence that they’re not exposed to emerging threats.


Gretel’s privacy engineering toolkit guards synthetic data against adversarial attacks
Gretel’s comprehensive offering enables users to classify, transform and generate synthetic data. Combined, these capabilities remove privacy bottlenecks for a myriad of development and workflow processes that prevent data sharing and stifle innovation


PingOne DaVinci provides no-code identity orchestration capabilities for enterprises
As the foundation of the PingOne Cloud Platform, DaVinci streamlines the integration and deployment of identity services through a no-code experience that makes it easier to design digital user journeys across multiple applications and ecosystems.


ShiftLeft Velocity Update enables application security and development teams to automate security controls
ShiftLeft announced a new release of its ShiftLeft CORE platform with a host of new features that enable application security and development teams to identify and remediate attackable vulnerabilities in the development process.


Tenable.cs updates enable organizations to detect and fix cloud infrastructure misconfigurations
Tenable.cs delivers full lifecycle cloud-native security to address cyber risks from build to runtime. With the new features, organizations can secure cloud resources, container images and cloud assets to provide end-to-end security from code to cloud to workload.


Juniper Secure Edge empowers customers to protect remote workforces from anywhere
Juniper Secure Edge provides Firewall-as-a-Service (FWaaS) in a single-stack software architecture featuring application control, intrusion prevention system (IPS), anti-malware, web proxy and filtering, and advanced threat protection.


Runecast adds OS analysis to help CIOs find and resolve issues within their IT infrastructures
Runecast has added OS analysis into its enterprise platform for proactive configuration and vulnerability management, security compliance, and remediation. The expanded capabilities build upon Runecast’s experience in providing users with deeper single-platform transparency into their hybrid environments – whether they are built from VMware, AWS, Azure or Kubernetes – together with proactive remediation to more efficiently fix discovered issues.


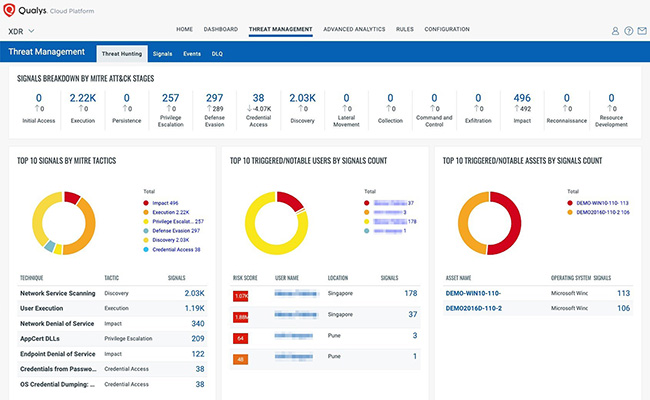
Prioritize threat detection and reduce alert fatigue with Qualys Context XDR
Qualys Context XDR provides the security context that operations teams need to eliminate false positives and noise by triangulating risk posture, asset criticality, and threat intelligence. Together, this provides visibility, contextual priority, and meaningful insights about the assets that allow teams to quickly make the most impactful decisions for enhanced protection.

Cybellum’s latest platform release enables product security teams to pinpoint threats and vulnerabilities
Release version 2.13 of Cybellum enables product and device manufacturers, and suppliers, to continuously detect, manage and remediate threats and vulnerabilities. With Cybellum, they can comply with regulations, minimize their risk posture, and get visibility into their supply chain.


SpinOne for Salesforce allows enterprises to secure and manage Salesforce data
Spin Technology is introducing a new solution, SpinOne for Salesforce, allowing organizations to protect their sales pipeline from data loss or corruption by backing up all objects and classifications.


DataStax’s new security capabilities in Astra DB prevents unauthorized access to sensitive PII data
DataStax announced that Astra DB now offers new levels of data access and security with new single sign-on (SSO) via SAML integration and data-at-rest security with self-managed encryption keys or bring your own keys (BYOK) encryption managed via a 3rd party KMS.


Gigamon’s new ThreatINSIGHT Guided-SaaS NDR provides visibility into historical network data
Gigamon announced the latest release of Gigamon ThreatINSIGHT Guided-SaaS NDR, giving incident responders a full year of metadata, prescriptive playbooks to automate the basics, and the ability for teams to work on the same case in parallel.


Cofense Validator identifies overlaps in email security controls
Cofense Validator works by sending real, in-the-wild phishing threats identified by Cofense through a customer’s SEG to see how effective it is at stopping those active threats. Customers realize instant ROI through reports with immediately actionable information.


Federal Reserve releases Synthetic Identity Fraud Mitigation Toolkit to help businesses fight fraud
The Federal Reserve released a Synthetic Identity Fraud Mitigation Toolkit to provide financial institutions, consumers and businesses with an online repository of insights and resources on synthetic identity fraud.


CoSoSys Endpoint Protector 5.5.0.0 strengthens data security for enterprises
In Endpoint Protector 5.5.0.0, it’s possible to define complex conditions for content scanning. This includes combining multiple criteria (such as PIIs, dictionary words, and regular expressions) using logical operators (AND/OR), and the ability to apply content detection rules only to specific file types (such as text files, Excel files, and more).


F5 Distributed Cloud Services improves modern application security
F5 announced a major expansion of its application security and delivery portfolio with F5 Distributed Cloud Services that provide security, multi-cloud networking, and edge-based computing solutions on a unified software-as-a-service (SaaS) platform.


Orca Security expands CIEM capabilities and multi-cloud security score
Orca Security’s context-aware engine unifies the intelligence collected from deep inside the workload with cloud configuration and infrastructure entitlement details to immediately surface risks and their root cause. Further updates to Orca Security include support for over forty compliance frameworks and Orca Security Score.


Bugcrowd PTaaS features deliver real-time visibility into testing progress
Bugcrowd PTaaS features include a rich dashboard with customer visibility into the progress of methodology-based pen tests–providing a 360-degree, real-time view for pen testers, customers, and Bugcrowd Security Engineers.


Mandiant Ransomware Defense Validation helps prevent specific ransomware attacks
Mandiant Advantage Ransomware Defense Validation leverages Mandiant’s threat intelligence, ransomware re-configuration capabilities and automated validation infrastructure to provide security leaders with evidence whether their organizations are able to prevent specific ransomware attacks.


Stellar Cyber Universal EDR optimizes event and alert data across different EDR products
Stellar Cyber’s Universal EDR delivers ready-to-consume EDR integration and data optimization without requiring the customer to complete manual integration, significantly speeding time to value. At the same time, Stellar Cyber enriches existing EDR security tools, allowing SOC teams to act quickly on findings from existing EDRs or enhancing that data with other critical alert data from other key systems (SIEM/NDR, etc.).


Blueshift XDR provides cybersecurity protection for SMB businesses
Blueshift XDR combines detection and prevention capabilities with a dedicated 24/7/365 US-based security-operations center to deliver cybersecurity protection to organizations of all sizes.


Verimatrix Secure Delivery Platform enables customers to protect their content and devices
The Verimatrix Security Delivery Platform is a cloud ecosystem that combines cybersecurity and anti-piracy services into a single pane of glass experience, providing value to media companies, content owners, streaming media providers, and broadcast operators worldwide.


Ondato OS provides enhanced process automation for financial institutions
Ondato OS provides organizations’ back office people with the tools to fully manage customer data, including task management across the employee team, risk scoring, profiling and case management. It provides key capabilities that are highly adaptable to customers’ needs, with a broad range of verification and signing options for individuals and legal entities.


Forcepoint ONE protects sensitive data across business applications and BYOD devices
The Forcepoint ONE all-in-one cloud platform simplifies security for both traditional and remote workforces, allowing users to gain safe, controlled access to business information on the web, in the cloud and in private applications.


NetSPI Attack Surface Management enhances security posture for organizations
NetSPI introduced Attack Surface Management to help secure the expanding, global attack surface. The platform features simple set-up, tracking and trending data over time, asset intelligence, Slack and email integrations, open-source intelligence gathering, asset, and exposure prioritization, port discovery, and more.


Arista Networks integrates NDR capabilities into the switching infrastructure
By embedding NDR capabilities into the Arista EOS-based switches themselves, customers derive broader visibility and threat hunting across the modern cognitive campus. The secure infrastructure optimizes existing human workflows and drives automated risk mitigation without the need to deploy additional and external network security products.


Sumo Logic Cloud SOAR enhancements increase automation for security teams
Sumo Logic announced new offerings for its Sumo Logic Cloud SOAR with the War Room and App Central features, adding more automation to drive important security operations activities.

MyCena launches mobile device add-on to protect organizations from cybersecurity breaches
MyCena’s Segmented Access Management solutions enables businesses to strengthen their digital access security by generating and distributing encrypted access credentials to the right users: ensuring only the legitimate user can access his or her credentials fortress through multiple levels of security.


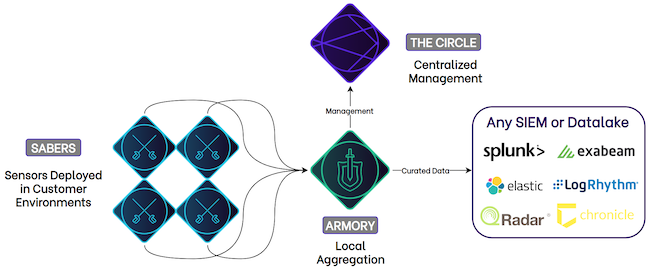
SynSaber 1.0 empowers operators to defend their industrial environments
SynSaber 1.0 is a small form factor solution that can be hosted on any existing infrastructure, even DIN-rail and edge devices. Once deployed within the operating environment, the vendor-agnostic “Sabers” send data to any collection point. With a robust yet flexible data pipeline, operators and analysts are now in control of monitoring and security.

Darktrace adds open investigations to Cyber AI Analyst platform
Cyber AI Analyst open investigations can be run manually by a human member of the security team or be triggered automatically by a third-party event, perhaps by an alert ingested directly from another security solution to validate and further contextualize their detections and decisions.

